Access Control without the Complexity
Access control, a critical requirement when integrating cloud datacenters, is also simplified with Cato. Once the cloud networks are connected, access is managed by our Firewall-as-a-Service, which has AD integration for granular user and application control built in, and full visibility for troubleshooting and auditing. There’s no need to settle for the insufficient ACL-level access control offered by Cloud providers or to invest in licensing and deploying 3rd party virtual FWs.
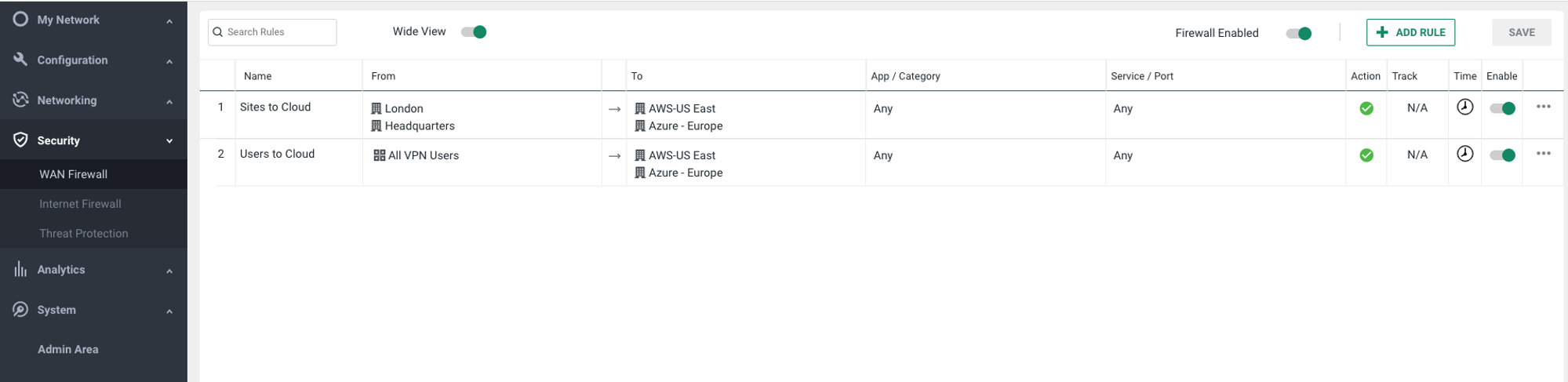
Cato's WAN Firewall Rules
Performance without the Premium Price Tag
Cato’s global private backbone saves you the cost of private connections and performance problems of backhauling to cloud datacenters by delivering end-to-end route optimization. Cato PoPs and cloud datacenter providers, such as AWS and Azure, share the same physical datacenters, practically eliminating the latency and packet loss between the two. That gives you similar performance of dedicated connections without the cost. With Cato, customers can see up to X4-X40 increase in throughput.
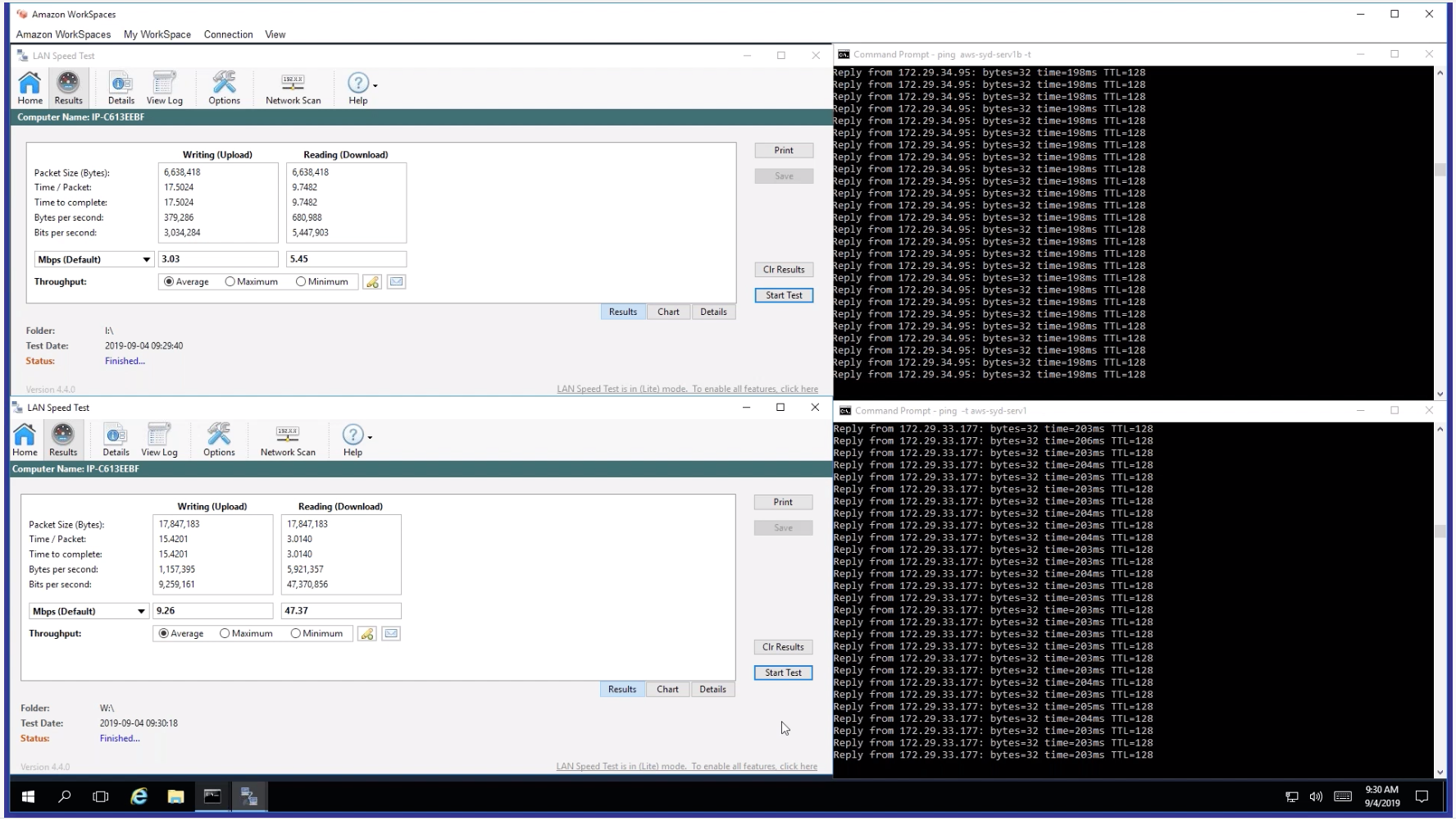
Performance test: Internet vs Cato
Security That’s Built In – Not Bolted On
The Cato’s Security-as-a-Service is built into the Cato private global backbone and delivered as a service. No additional appliances (physical or virtual) need to be purchased or deployed. Cato has a single security stack covering all of your cloud datacenters, physical locations, and remote workers. All of your network traffic, regardless of where it’s coming from, is processed through our NGFW, SWG, IPS, NGAM and MDR. As more load is put on the cloud datacenter, or a new cloud datacenter is added, the service seamlessly scales without any need to buy additional security solutions or upgrade existing ones.

Full Visibility for Full Control
By making the cloud datacenter a native part of the enterprise network, Cato gives you the exact same visibility and control as you have with your physical network, without any additional components. Cato provides a single-pane-of-glass into the complete enterprise network — sites, cloud resources, and mobile users for networking and security — through its cloud-based management application. Through the application, customers can control all parts of the service, including network and security policy configuration, detailed network analytics, and security event reporting.
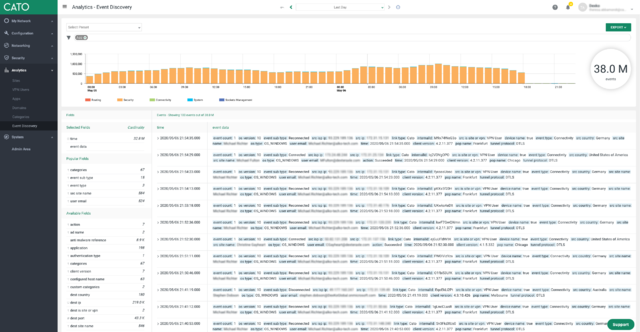
Cato's Event Discovery

